HIPAA Compliant Healthcare Applications, Part 1: What You Need to Know About User Authentication
- Pablo Bullian
- June 12, 2017

Updated on July 23, 2020.
Of the three main components of HIPAA (the Privacy Rule, Security Rule, and Breach Notification Rule) the Security Rule is particularly relevant to healthcare mobile app development. The majority of these applications, from patient portals to mhealth apps, store or transmit electronic protected health information (ePHI). It’s essential to keep this information safe, and the Security Rule has in-depth guidance on the extent to which this needs to be accomplished, but with a fair amount of flexibility as to the strategies for implementation.
Here, we decode the Security Rule as it applies to the patient portal and mHealth app development, specifically in regards to user authentication. In Part 2 of this series, we cover auditing, and in Part 3, we discuss issues related to data transfer, such as encryption and notifications.
What is an Appropriate Level of Authentication for Online Patient Access to Health Information?
During HIPAA compliant healthcare application registration, healthcare organizations need to set up procedures that verify the person’s identity requesting access to ePHI. There is a false belief that the only way to ensure the user is who they claim to be is for registration to be done in person, within the practice — aided by a staff member. While this is an option — considered outdated by some — it is not a HIPAA requirement. An alternative option is for a patient to provide an email address over the phone and receive an invitation to register for the healthcare mobile app platform. Providing your email address in person is considered more credible than most setup authentications on the web, where the email address is entered into a registration form. Patients could also register autonomously, also referred to as self-registration. While these two remote options are less secure than in-person authentication, they are preferred for convenience. Additional verification can be added by asking the patient challenge questions produced by a 3rd party such as IDology during registration.
A simplified registration process increases healthcare application use, such as a patient portal. And increased patient portal use results in improved patient engagement, more efficient patient appointment scheduling and cancellations, and enhanced treatment plan adherence.
At Bridge Patient Portal, one of the most common complaints made by healthcare organizations using other patient portals (typically bundled with their EHR vendor) is the cumbersome process patients must undergo to register.
Read More: Understanding Mobile App HIPAA Compliance
Is Multi-factor Authentication Necessary?
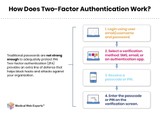
Multi-factor authentication is defined as requiring a patient to produce more than one type of credential when logging into an application. The majority of logins only need a user to enter information such as a username and password. In multi-factor authentication, additional information is required such as a code on a card, security token, SMS message, and/or by direct verification of identity, like a fingerprint or challenge questions. As passwords and access to email accounts can easily be compromised, multi-factor authentication is growing in popularity for healthcare mobile app platforms. While the HIPAA Security Rule does not require multi-factor authentication, it is important to thoroughly consider its provisions on information access management and access control to determine how to best account for them in your HIPAA compliant healthcare application.
How Strong Do Passwords Need to Be?
More and more mobile app platforms now require users to adopt “strong” passwords. While HIPAA requires the use of passwords, there is no legal specification on password strength. Therefore, each healthcare organization can decide on password requirements during the application development phase. We recommend following the NIST Digital Identity Guidelines, which recommends that a password should be between 8 to 64 characters long, and all ASCII characters, including the space character, are acceptable.
It’s also essential that when a user creates or changes a password, it be tested against the following:
- Passwords obtained from previous data breaches (One can check if an account has been compromised in a data breach on a website such as https://haveibeenpwned.com/.)
- Dictionary words.
- Repetitive or sequential characters (e.g. “aaaaaa” or “1234abcd”)
- Context-specific words, such as the name of the service, the username, and derivatives thereof.
How Should Passwords Be Managed and Monitored?
HIPAA does include addressable implementation specifications on password management and login monitoring. Addressable means that an organization can decide to implement the specification as is, choose to put an alternate security measure or measures in place, or even — if the specification is not reasonable or appropriate to the particular entity — implement nothing. The key is that the decision and reasoning behind the implementation must be documented in written form, with in-depth consideration and appropriate justification demonstrated.
In this case, HIPAA stipulates that Covered Entities and Business Associates include several important features in their security awareness programs. One is to train staff on procedures for creating, changing, and safeguarding passwords. The other is that staff also learn how to monitor login attempts by external users and report any potentially problematic login activity, such as failed login attempts. Each organization needs to fully consider these addressable matters to plan, document, and implement its strategy.
What Are the Login Timeout Requirements, and How Does This Apply to a Personal Mobile Device?
HIPAA includes automatic logoff — when the application ends a user’s session after a specific period of inactivity — as another addressable implementation specification. However, the time to logoff is not stated. In choosing the number of minutes of allowed inactivity before a session is terminated, it’s essential to consider on what device and in what environment the application will be used. If you’re working with a mhealth app or HIPAA compliant messaging that will be used by patients on their phones anywhere they go, including crowded areas, a short time to logout of 2 to 3 minutes is advisable. However, if you’re working on the physician’s side of an application used in a private doctor’s office, a longer time to log out, like 10 to 15 minutes, is acceptable.
After a predetermined period of inactivity, a patient is required to re-enter their long-form, complex, secure password. Biometric authentication simplifies the login process and allows patients to seamlessly verify their identity through fingerprint or facial recognition technology before accessing the HIPAA compliant healthcare application.
We’ve only scratched the surface of the Security Rule. Check out Part 2 (HIPAA auditing) and Part 3 (encryption, servers, and notifications to patients).